usd-2020-0051 | Gophish v0.10.1
Advisory ID: usd-2020-0051
CVE Number: CVE-2020-24711
Affected Product: Gophish
Affected Version: v0.10.1
Vulnerability Type: Improper Restriction of Rendered UI Layers or Frames
Security Risk: Medium
Vendor URL: https://getgophish.com/
Vendor Status: Fixed
Description
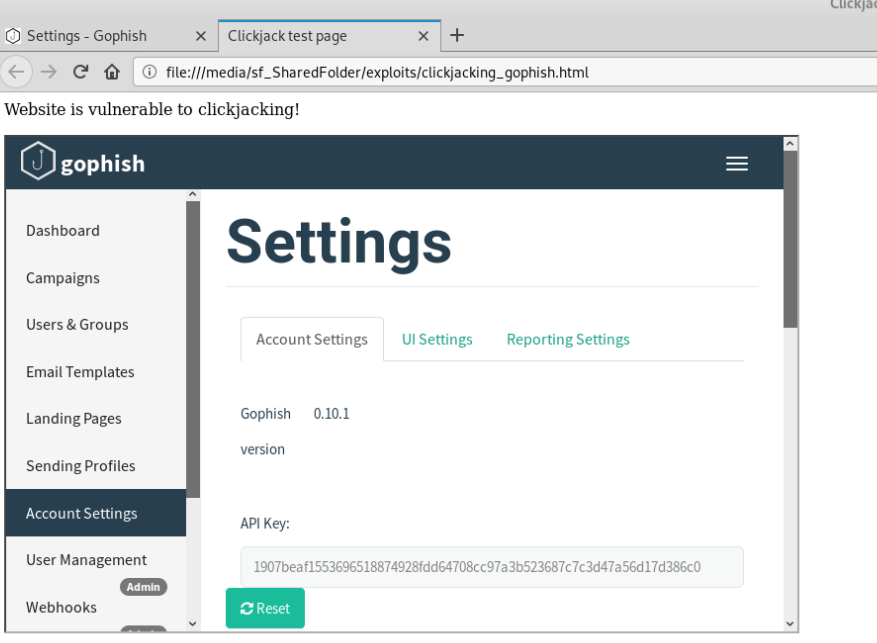
Gophish is vulnerable to clickjacking attacks. As can be seen in the screenshot below, it is the Reset button on the Account Settings page that is affected by this vulnerability. Since the Reset button resets the API key of the phishing framework, this vulnerability could enable and attacker to cause denial-of-service for services that are dependent on Gophish’s API.
Proof of Concept (PoC)
Fix
It is recommended to use the frame-ancestors directive of the Content-Security-Policy header to prohibit a browser from rendering the content of the page inside an iframe. Alternatively, the same can be achieved by using the X-Frame-Options header. In both cases, the response header has to be set on every page to guarantee a proper protection against the attack. The exclusive use of framekiller JavaScript is discouraged. Detailed information on protection against clickjacking attacks can be found at OWASP: Clickjacking Defense Cheat Sheet.
Timeline
- 2020-06-18 First contact request via security@getgophish.com
- 2020-06-22 Vendor responds to initial contact
- 2020-08-07 Vendor publishes a fix
- 2020-09-29 Security advisory released
Credits
This security vulnerability was found by Marcus Nilsson of usd AG.